Featured
Table of Contents
Vpns, Tor, I2p — How Does Nym Compare?
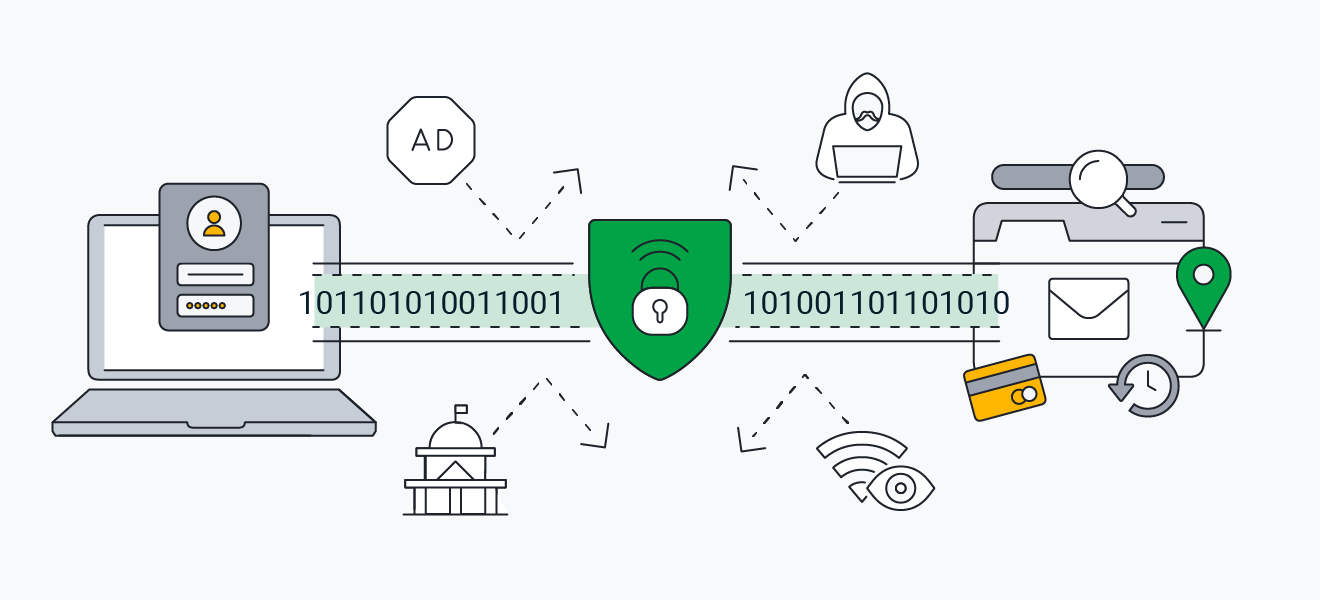
Do you ever question who can see your internet traffic while surfing the web? If so, you're not alone.
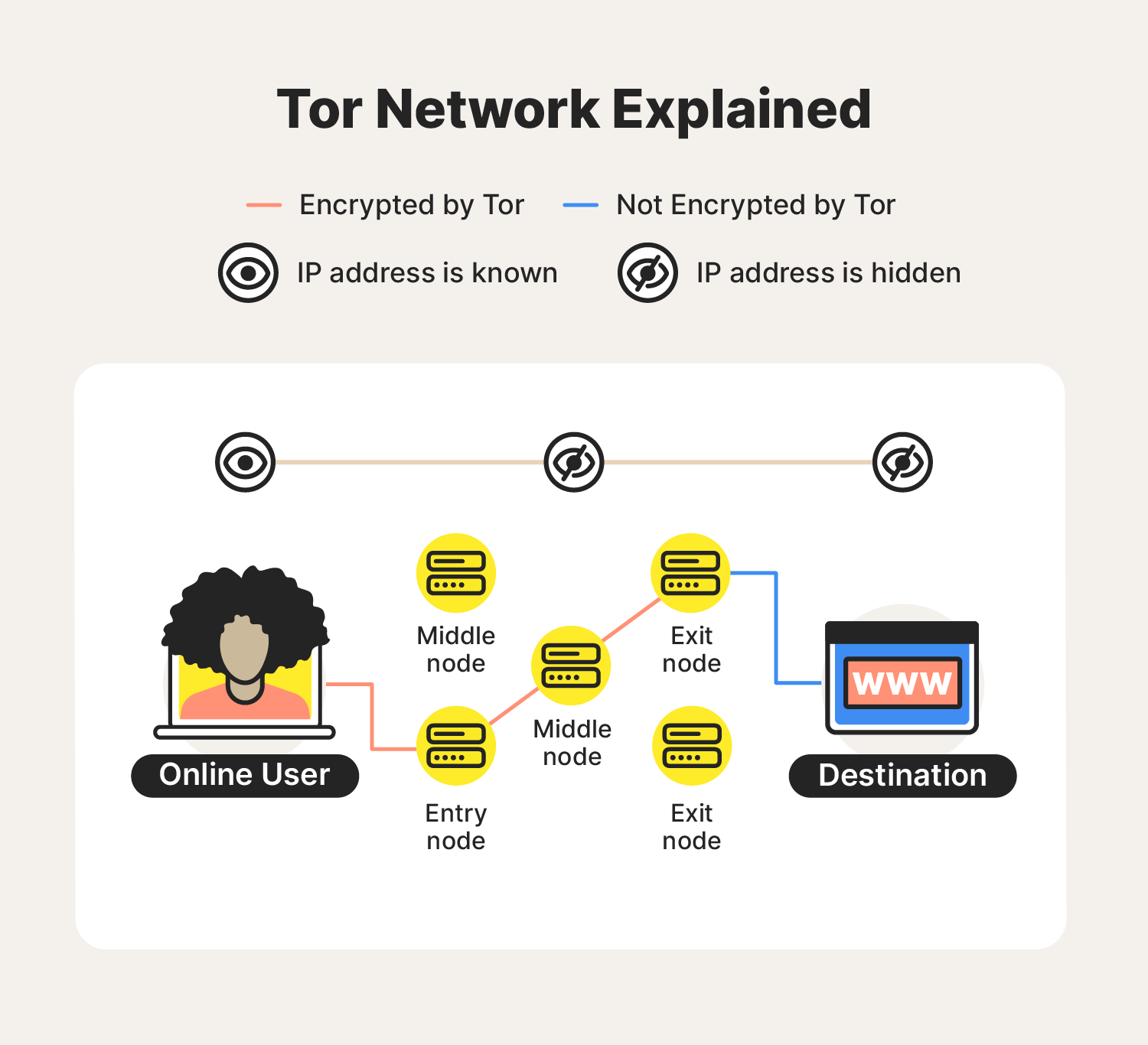
By using these tools, internet users can use the web with improved peace of mind. The middle node then gets rid of the 2nd layer of encryption and sends your demand to the exit node. The exit node removes the last layer of file encryption, permitting it to see your demand, although it will be not able to determine who requested it.
Tor Vs Vpn: What Are The Differences? Which One Is Better?
The only way someone can identify your activity is if they took place to preserve both of the randomly picked guard and exit nodes, which is extremely not likely. While using the Tor internet browser has its perks, there are advantages and disadvantages when it comes to utilizing Tor over a standard browser like Safari or Google Chrome.
Pros of utilizing the Tor browser: Free and easy to download: Thanks to various anonymous volunteers, users can easily download and utilize the Tor browser free of charge. Difficult to close down: The Tor network is run by thousands of volunteers all over the world, making it extremely difficult for a single entity to shut it down.
Bypass censorship: If you remain in a country with stringent censorship, the Tor web browser will enable you to bypass censorship and go to obstructed sites. Access to the dark web: With the Tor browser, you're able to gain access to sites on the dark web. These sites are also referred to as onion sites and can only be checked out using the Tor web browser.
Tor Vs. Vpn: What's The Difference Between Them? ...
Node vulnerability: Because the Tor internet browser assists make your identity confidential, it doesn't bother securing your information after it leaves the exit node. This makes it possible for someone monitoring your connection to see your traffic information, even if they do not understand who it belongs to. Even with its benefits and drawbacks, there are certain scenarios in which utilizing the Tor internet browser could be your finest alternative.
Now that you're aware of the advantages and downsides of using Tor, you may be wondering when you need to use it. Tor is best for: Confidential web searching Accessing the dark web Untraceable communication If your primary top priority is staying anonymous online or you wish to access the dark web, then using the Tor web browser may be your best choice.
This allows VPN users to cruise the web privately and anonymously, no matter the internet connection. A VPN will also conceal your IP address and secure your internet traffic. So, how does a VPN work? Your internet traffic is encrypted and sent out to a remote server to disguise your IP address.
Tor Vs Vpn: What's The Difference And Which Is Safer?
This same procedure takes place with the information returning to your device. Just like using the Tor web browser, VPNs aren't best.
Follow along to find out when utilizing a VPN is your finest option. After finding out more about VPNs, you might be wondering when to use one.
Before picking a VPN or Tor, follow along to learn more about the key differences. A VPN is a centralized service, indicating the VPN provider is the sole authority, managing all servers and connections.
Vpn Vs. Tor – Which One Is Better?
On the other hand, Tor is totally decentralized, and none of its servers are controlled by a single entity. Rather, the decentralized network counts on its international network of individual volunteers. Because of this, it is a lot more hard for somebody to trace your information or closed down the network.
Most VPNs direct your web traffic through a single server before it reaches its intended location. When it comes to picking a VPN, you'll have numerous alternatives to pick from.
This grants you all of the privacy benefits of the Tor network and additional IP address defense from your VPN, preventing your ISP from understanding that you utilize Tor and keeping any Tor node from seeing your IP address. Tor then VPN: Beginning with the Tor network is a challenging process and may not be supported by all VPN providers.
Tor Vs Vpn - What's The Difference? (And Which Should You ...
When you utilize a VPN, you need to rely on the VPN service supplier. Since each Tor node only knows the identity of the server before it, it is difficult for anyone to reverse engineer your connection's route through the Onion network. Tor also lets you access a number of unlisted sites with the.
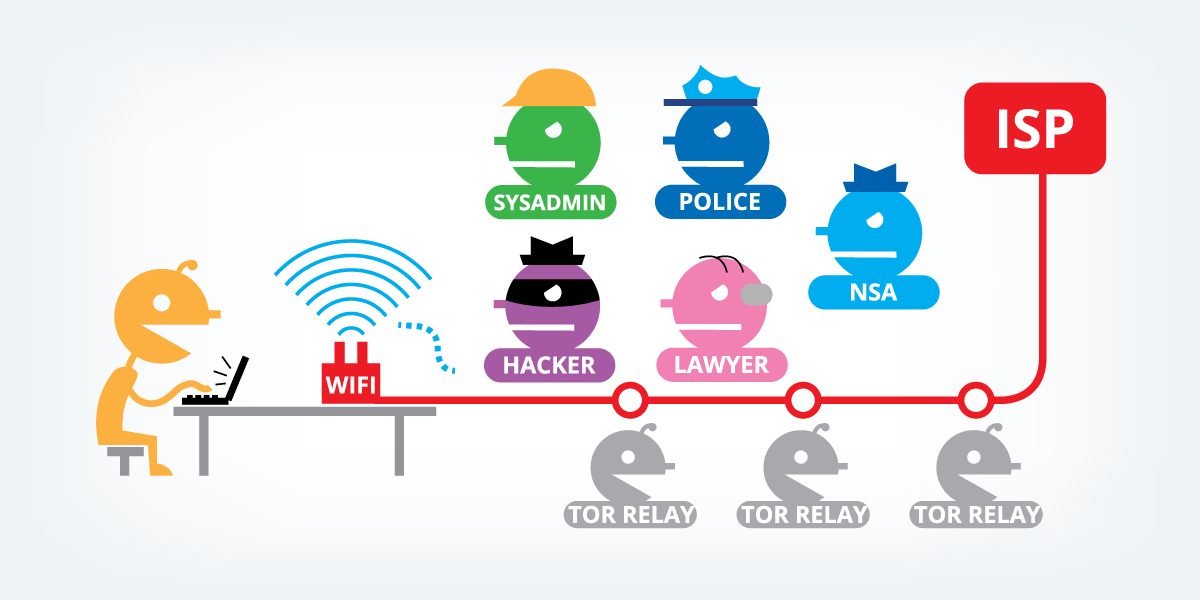
VPNs do not need the exact same level of technical efficiency as utilizing Tor does. If you're brief on time, here are some fast responses to common questions asked about Tor vs.This makes VPNs the preferred method of bypassing geo-restrictions. Users can choose to utilize a VPN with Tor for an additional layer of security.
Latest Posts
10 Best Business Vpn Services [2023]: A Comprehensive ...
Best Virtual Private Networks Reviews 2023
Best Vpns For Android - All About Cookies