Featured
Table of Contents
- – Internet Protocol Security Explained
- – Ipsec Configuration - Win32 Apps
- – 7 Common Vpn Protocols Explained And Compared
- – What Is Internet Protocol Security (Ipsec)?
- – What Is Internet Protocol Security? Applicati...
- – What Is The Ikev2/ipsec Vpn Protocol? How Do...
- – What Is Ipsec? - Internet Protocol Security ...
- – How Ipsec Works, It's Components And Purpose
- – Ipsec Vpns: What They Are And How To Set The...
- – What Is Ipsec? Definition & Deep Dive
Internet Protocol Security Explained
IPsec (Internet Protocol Security) is a structure that helps us to secure IP traffic on the network layer. IPsec can secure our traffic with the following features:: by securing our information, no one other than the sender and receiver will be able to read our data.

By determining a hash worth, the sender and receiver will have the ability to check if modifications have actually been made to the packet.: the sender and receiver will verify each other to make certain that we are actually talking with the gadget we mean to.: even if a packet is encrypted and authenticated, an aggressor could attempt to capture these packages and send them again.
Ipsec Configuration - Win32 Apps
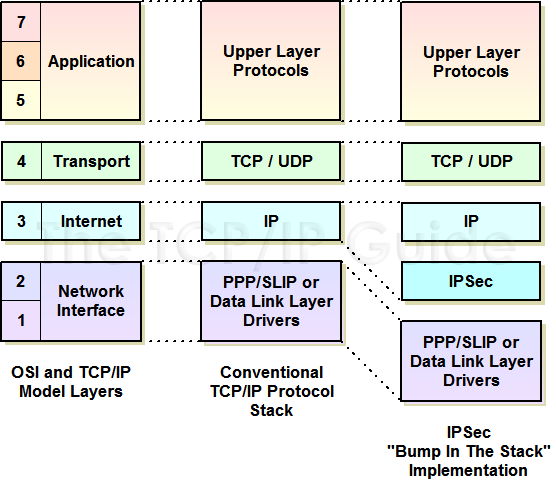
As a framework, IPsec uses a range of protocols to carry out the features I described above. Here's an introduction: Do not stress over all the boxes you see in the picture above, we will cover each of those. To give you an example, for file encryption we can pick if we want to utilize DES, 3DES or AES.
In this lesson I will begin with a summary and then we will take a better look at each of the elements. Before we can safeguard any IP packages, we require 2 IPsec peers that develop the IPsec tunnel. To develop an IPsec tunnel, we utilize a procedure called.
7 Common Vpn Protocols Explained And Compared
In this phase, an session is established. This is also called the or tunnel. The collection of criteria that the 2 gadgets will use is called a. Here's an example of two routers that have developed the IKE phase 1 tunnel: The IKE phase 1 tunnel is only utilized for.
Here's a photo of our two routers that completed IKE phase 2: Once IKE stage 2 is finished, we have an IKE phase 2 tunnel (or IPsec tunnel) that we can use to protect our user information. This user data will be sent through the IKE phase 2 tunnel: IKE develops the tunnels for us however it does not verify or secure user data.
What Is Internet Protocol Security (Ipsec)?

I will discuss these 2 modes in information later on in this lesson. The whole procedure of IPsec includes 5 steps:: something needs to trigger the creation of our tunnels. For instance when you configure IPsec on a router, you utilize an access-list to tell the router what information to secure.
Everything I describe below applies to IKEv1. The primary function of IKE stage 1 is to develop a safe tunnel that we can use for IKE stage 2. We can break down stage 1 in 3 basic actions: The peer that has traffic that needs to be secured will initiate the IKE stage 1 negotiation.
What Is Internet Protocol Security? Applications And Benefits
: each peer has to show who he is. 2 commonly used choices are a pre-shared secret or digital certificates.: the DH group figures out the strength of the secret that is used in the essential exchange process. The greater group numbers are more secure however take longer to compute.
The last action is that the 2 peers will verify each other using the authentication technique that they concurred upon on in the negotiation. When the authentication is effective, we have completed IKE stage 1. Completion result is a IKE phase 1 tunnel (aka ISAKMP tunnel) which is bidirectional.
What Is The Ikev2/ipsec Vpn Protocol? How Does It Work?
This is a proposal for the security association. Above you can see that the initiator uses IP address 192. 168.12. 1 and is sending out a proposition to responder (peer we wish to link to) 192. 168.12. 2. IKE utilizes for this. In the output above you can see an initiator, this is a distinct value that recognizes this security association.
The domain of analysis is IPsec and this is the first proposition. In the you can find the qualities that we want to use for this security association.
What Is Ipsec? - Internet Protocol Security Explained
Because our peers agree on the security association to use, the initiator will start the Diffie Hellman key exchange. In the output above you can see the payload for the essential exchange and the nonce. The responder will likewise send out his/her Diffie Hellman nonces to the initiator, our two peers can now determine the Diffie Hellman shared key.
These 2 are used for recognition and authentication of each peer. The initiator begins. And above we have the 6th message from the responder with its identification and authentication info. IKEv1 primary mode has now completed and we can continue with IKE phase 2. Before we continue with phase 2, let me show you aggressive mode initially.
How Ipsec Works, It's Components And Purpose
1) to the responder (192. 168.12. 2). You can see the change payload with the security association qualities, DH nonces and the recognition (in clear text) in this single message. The responder now has whatever in needs to create the DH shared crucial and sends some nonces to the initiator so that it can likewise calculate the DH shared key.
Both peers have everything they need, the last message from the initiator is a hash that is used for authentication. Our IKE phase 1 tunnel is now up and running and we are all set to continue with IKE phase 2. The IKE phase 2 tunnel (IPsec tunnel) will be in fact used to protect user information.
Ipsec Vpns: What They Are And How To Set Them Up
It secures the IP package by calculating a hash value over nearly all fields in the IP header. The fields it omits are the ones that can be changed in transit (TTL and header checksum). Let's begin with transport mode Transportation mode is basic, it simply includes an AH header after the IP header.
With tunnel mode we include a new IP header on top of the original IP packet. This might be useful when you are using private IP addresses and you require to tunnel your traffic over the Web.
What Is Ipsec? Definition & Deep Dive
Our transportation layer (TCP for instance) and payload will be secured. It likewise uses authentication but unlike AH, it's not for the entire IP package. Here's what it appears like in wireshark: Above you can see the original IP package which we are using ESP. The IP header is in cleartext however whatever else is encrypted.
The original IP header is now likewise encrypted. Here's what it appears like in wireshark: The output of the capture is above is comparable to what you have seen in transportation mode. The only difference is that this is a brand-new IP header, you don't get to see the initial IP header.
Table of Contents
- – Internet Protocol Security Explained
- – Ipsec Configuration - Win32 Apps
- – 7 Common Vpn Protocols Explained And Compared
- – What Is Internet Protocol Security (Ipsec)?
- – What Is Internet Protocol Security? Applicati...
- – What Is The Ikev2/ipsec Vpn Protocol? How Do...
- – What Is Ipsec? - Internet Protocol Security ...
- – How Ipsec Works, It's Components And Purpose
- – Ipsec Vpns: What They Are And How To Set The...
- – What Is Ipsec? Definition & Deep Dive
Latest Posts
10 Best Business Vpn Services [2023]: A Comprehensive ...
Best Virtual Private Networks Reviews 2023
Best Vpns For Android - All About Cookies
More
Latest Posts
10 Best Business Vpn Services [2023]: A Comprehensive ...
Best Virtual Private Networks Reviews 2023
Best Vpns For Android - All About Cookies